Evaluating risk with PingOne Protect
PingOne Advanced Identity Cloud PingAM Android iOS JavaScript
You can integrate PingOne Protect into your apps to evaluate the risk involved in a transaction.
|
PingOne Protect is supported in the following servers:
|
Figure 1. A flowchart illustrating how risk predictors evaluate many different data points.
Your app can gather information during a transaction, return this information to PingOne Protect, and request a risk evaluation.
Based on the response from PingOne Protect, you can choose whether to allow or deny the transaction or perform additional mitigation, such as bot detection measures.
You can use the audit functionality in PingOne to view the risk evaluations:
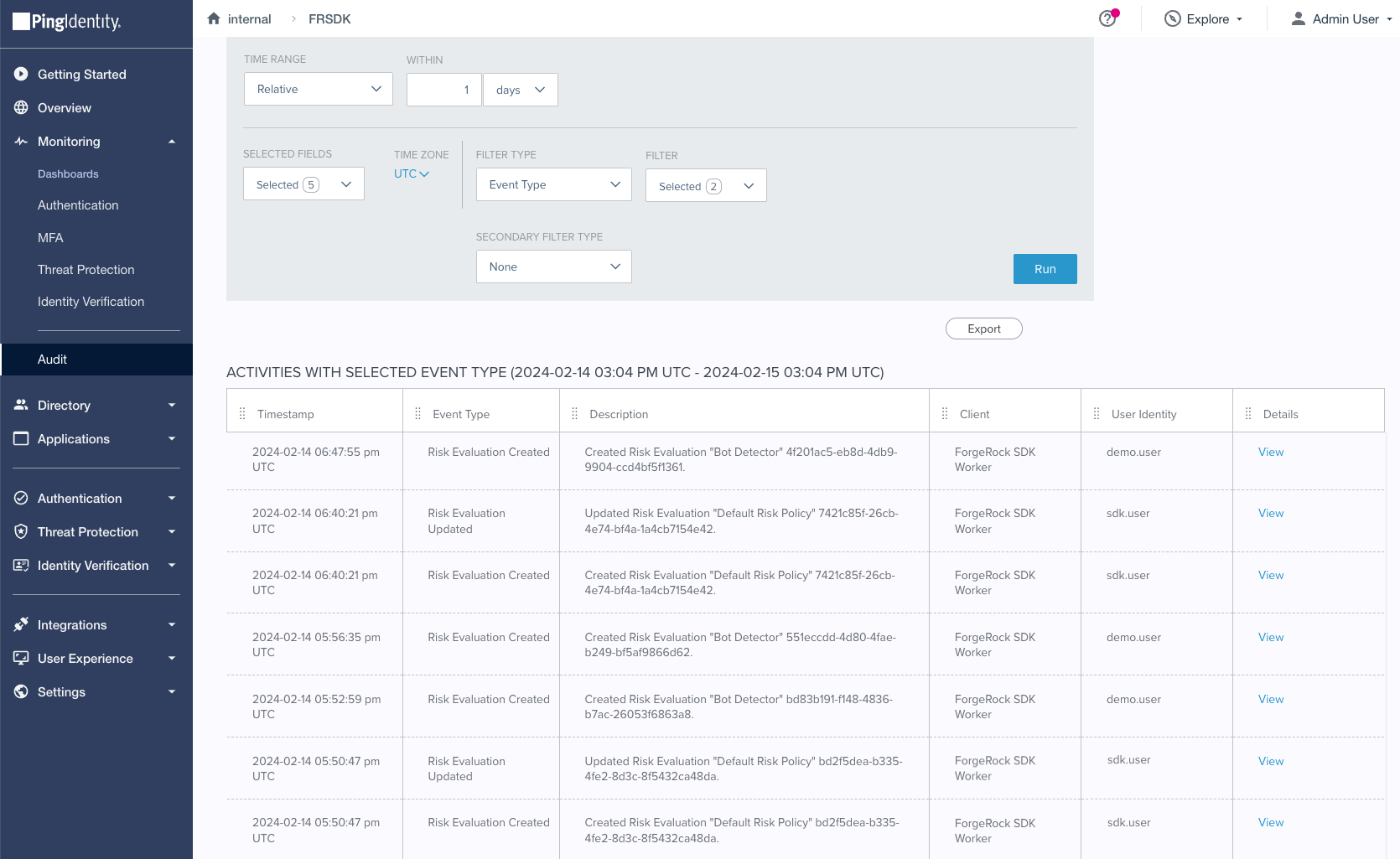
Figure 2. Risk evaluation records in the PingOne audit viewer.