Preparing Advanced Identity Cloud or PingAM for FIDO in iOS
PingOne Advanced Identity Cloud PingAM iOS
Before enabling FIDO authentication in your iOS apps you must complete the following tasks:
Step 1. Associating your iOS app with your Advanced Identity Cloud or PingAM server
You can create an apple-app-site-association file that creates a secure association between your domain and your app. This allows you to share credentials, and use universal links to open your app from your website.
To create the secure association, you upload the apple-app-site-association file to your domain, and add matching Associated Domains Entitlement keys to your app.
Preparing a site association file
-
Prepare a JSON-formatted file named
apple-app-site-association, as shown below.Ensure you include the
webcredentialsentitlement{ "applinks": { "details": [ { "appIDs": [ "XXXXXXXXXX.com.example.AppName" ], "components": [ { "/": "/reset/*", "comment": "Success after reset password journey" } ] } ] }, "webcredentials": { "apps": [ "XXXXXXXXXX.com.example.AppName" ] } } -
Replace XXXXXXXXXX.com.example.AppName with the app ID of your client iOS application.
Learn more in Supporting associated domains in the Apple Developer documentation.
Hosting apple-app-site-association files in Advanced Identity Cloud or PingAM
-
For PingOne Advanced Identity Cloud deployments, refer to Upload an iOS apple-app-site-association file.
-
For self-managed PingAM deployments, host the file at
https://<your domain>/.well-known/apple-app-site-association.
|
Make a note of the domain where you uploaded the file, as you’ll need to add matching Associated Domains Entitlement keys to your iOS project. |
Step 2. Configuring authentication journeys for FIDO on iOS
Configure authentication journeys for FIDO2 on iOS
Authentication journeys for FIDO primarily use these nodes:
- WebAuthn Registration Node
-
Handles the creation and storage of new passkeys.
- WebAuthn Authentication Node
-
Manages the sign-in process by issuing and verifying challenges.
Learn more about creating authentication journeys for FIDO in Journeys for WebAuthn.
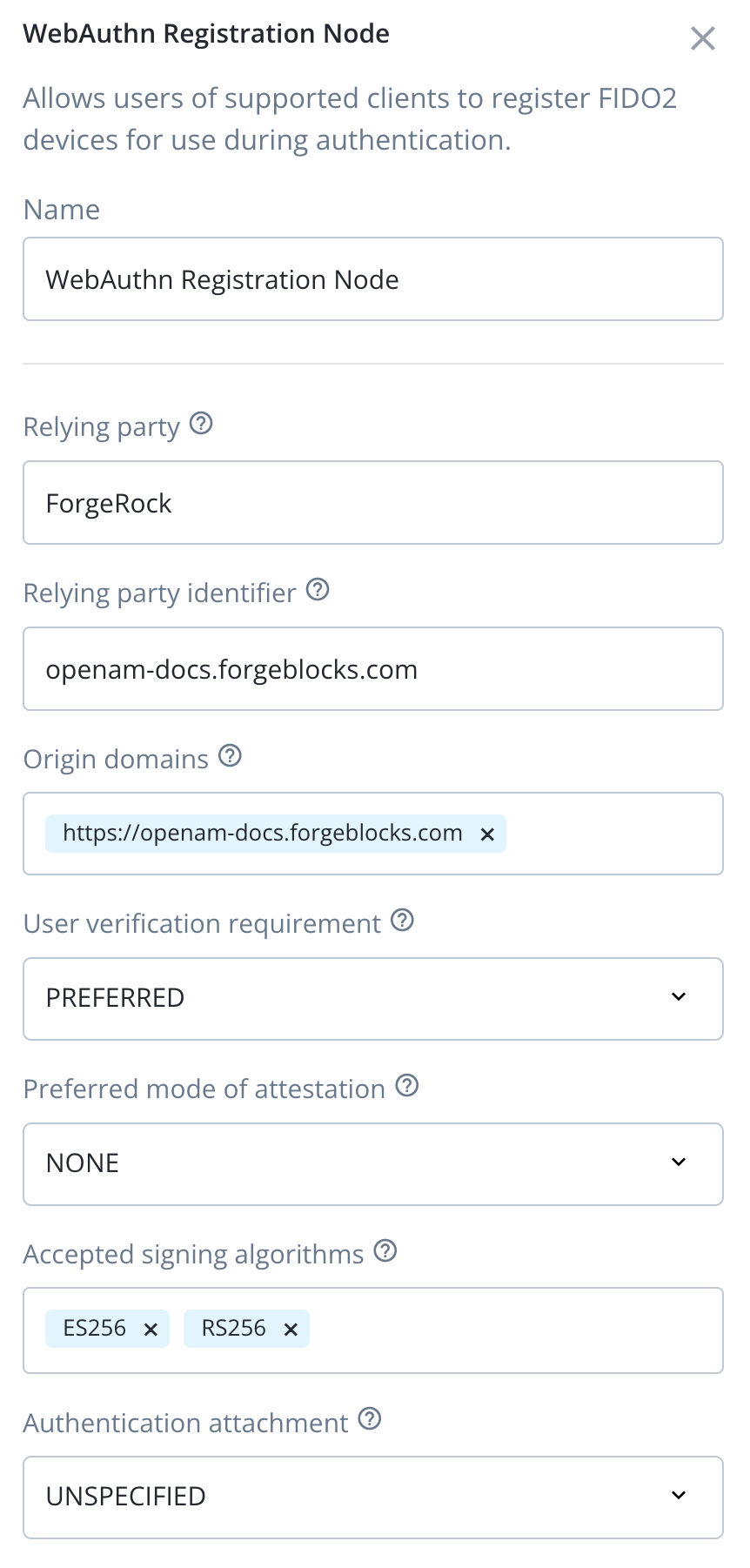
To prepare your authentication journeys to use FIDO with an iOS application, you need to configure each WebAuthn Registration node and WebAuthn Authentication node in your authentication journey to work with your iOS app.
|
You must use the same configuration values in each WebAuthn Registration node and WebAuthn Authentication node in the journey. Any mismatches in configuration between these nodes will cause authentication to fail. |
- Each WebAuthn Registration node and WebAuthn Authentication node
-
-
In Origin domains:
-
To enable Passkey support, add the fully-qualified domain name of the Advanced Identity Cloud or PingAM instance as an origin domain. For example,
https://openam-docs.forgeblocks.com.
-
-
Ensure the Return challenge as JavaScript option is not enabled.
The SDK expects a JSON response from these nodes, enabling this option would cause the journey to fail.
-
In Relying party identifier, enter the domain hosting the
apple-app-site-associationfile you create and uploaded.For example,
openam-docs.forgeblocks.comYou do not need the protocol or the path.
-
- Every WebAuthn Registration node
-
-
In Accepted signing algorithms, include one or more of
ES256andRS256. -
Ensure the Limit registrations option is not enabled.
-
The result will resemble the following:
Next steps
You can now proceed to Integrating FIDO auth journeys in iOS.